10 ways malicious attackers spy on your mobile data traffic
In a world where we increasingly rely on permanently connected mobile devices, we should be aware of the ways our private information is vulnerable to thieves and snoops. There are various reasons to spy on mobile: criminals steal credit cards details, businessmen want to know the secrets of their competition and some people like to control their personal relationships.
This article will explain 10 ways, some common and some not, in which criminals or enemies might steal and spy on your secrets via your mobile.
We will suggest techniques to protect yourself from common forms of online spying, so that you can actually feel safer and more secure with your mobile devices and computers.
1. Open Public Wi-Fi

You come to a coffeeshop, get a cup of coffee, sit down and connect your phone to the public wi-fi. Little do you know that a guy sitting at the next table is intercepting your web traffic. Scary? Yes! Possible? Very easily.
A network sniffer such as Wireshark can easily intercept all communications on an unprotected wi-fi network. Even when the coffeeshop wi-fi is secured with a WEP or a WPA/WPA2 password, the intercepted communications can be deciphered.
What if you only use your secure home wi-fi? Many old routers still use WEP encryption which is notoriously easy to break. An attacker in the apartment next door can discover your WEP password as a matter of minutes. They can also try to guess your password if the network encryption is strong.
How to protect yourself:
- Make sure you use HTTPS protocol when entering any password or sensitive information on a public wi-fi.
- Only use WPA2 encryption on your home router and pick a secure, hard to guess password. Never keep the default password that came with your router.
2. Cell phone spy apps that spy on your mobile
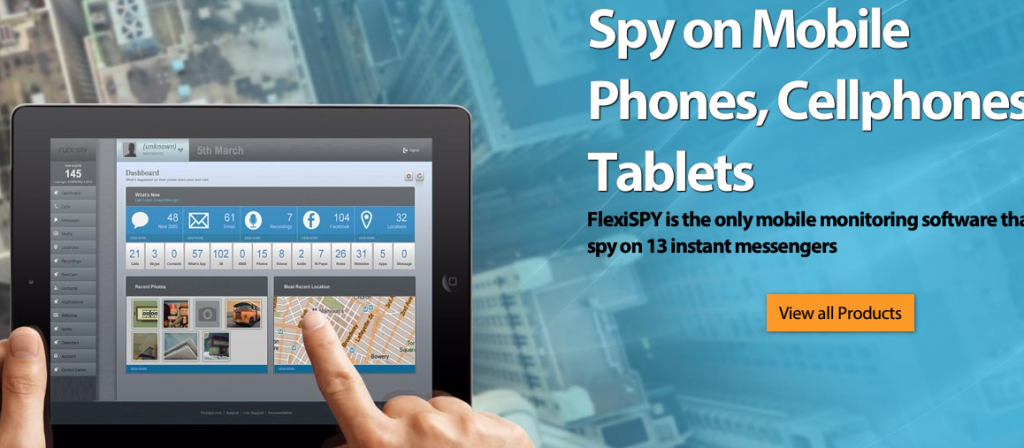
Modern cell phone spy apps, such as FlexiSPY and mSpy, are consumer products that are very easy to install for a potential s. Once such a spy app runs on your phone, it reports back everything – starting from your e-mails and chats in practically any messaging application (WhatsApp, Facebook, etc.) and ending with recording your calls and intercepting your calls as they happen.
The capabilities that we saw in FlexiSPY are simply incredible for a consumer product – you’d think that only a government agency would have access to such a powerful SMS tracker and phone spy. Of course, using such an app for spying on an individual is illegal in most jurisdictions, but it’s not going to console you if your personal data would be stolen.
How to protect yourself:
- Keep your phone locked and don’t tell your passcode to anyone. Don’t leave your phone unattended. Installing a mobile spy app will only take minutes and once it runs on your phone, it’s very difficult to detect.
- If you suspect anything – backup all your data and restore the phone to factory settings.
3. Rogue cell towers
Now, let’s say that you’re not using any public wi-fi for accessing your bank account. You only use 3G. 100% secure? Not exactly.
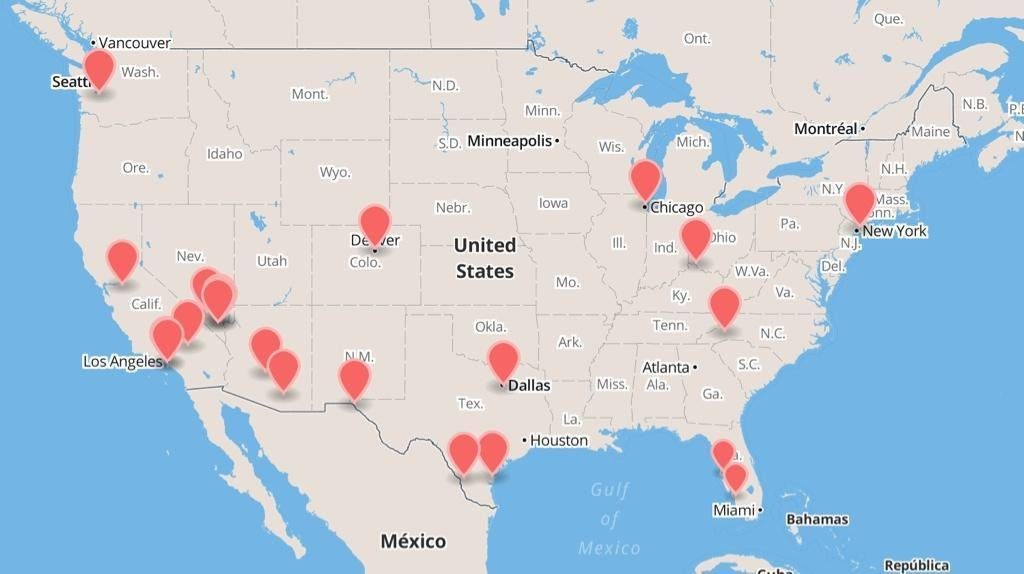
In August 2014, GSMK – a German firm developing ultra-secure phones for the corporate market – reported that its phones had identified multiple rogue cell towers in various locations across in the US. It’s not clear who operates the rogue cell towers, but it’s clear that this technology is available to criminal gangs.
UPDATE:
In December 2014, a Norwegian newspaper Aftenposten reported that fake mobile base stations have been detected around the Norwegian parliament in Oslo – probably stationed there to spy on politicians.
A rogue cell tower can be both fixed and portable(can be operated from a van). It operates as a GSM interceptor by emitting a stronger signal than the legitimate cell towers, and thus making phones in its vicinity to connect to it. Once the nearby phones have been tricked into connecting to a fake cell tower, it acts as a “man in the middle” – a proxy that transmits all communication back and forth to a legitimate cell towers, but grabs all the juicy parts – passwords, bank accounts and secret information.
How to protect yourself:
Difficult to defend against a rogue cell tower other than to buy a $3000 Cryptophone.
4. Rogue Mobile Network Employee
In 2005, Vodafone Greece discovered that more than 100 mobile phones belonging to local politicians and civil servants have been tapped. The wiretap has been setup by exploiting Ericsson switches serving the Vodafone Greece network. The perpetrators have never been found, though a high-level manager in Vodafone Greece has committed a mysterious suicide shortly after the scandal had broke.
This case demonstrates that it doesn’t take a powerful government to spy on your mobile phone. A rogue employee of your mobile network operator can snoop on your calls and data. It is not easy to do, since cellular companies log all such activity of their employees, but still possible. Some employees will always know their way in the system inside out and will be open to offers that “they can’t refuse”.
5. Malware

Different reports have found that 30% to 50% of all computers in the world are infected with some kind of malware. Most modern malware sits quietly on the infected computer, collects passwords and credit card numbers and sends them discreetly “home” – to the criminal gangs. Criminals use the stolen credentials to commit financial fraud and to hack email, social media and bank accounts.
Malware is also very common on Android phones, where it can disguise itself as a legit application downloadable from the Google Play store. For each malicious app that Google removes from the store, a couple of new ones take its place. These days users are used to apps asking for seemingly unrelated permissions. So, let’s say, a game, can ask during its installation for a permission to access the file system, the contact list and SMS messages. This fake “game” will send your text messages to a server where the malware owner will be able to access it.
How to protect yourself:
- Always update your operating system on your computer. Don’t run any applications that you’re not familiar of.
- If you’re an Android user, make sure that your apps only have the permissions that they need. For example, don’t install a game that needs access to your contact list.
- Periodically scan all your devices with a good malware detector.
6. Weak passwords

Probably the most common way to steal personal information is exploiting weak passwords. Hackers have ways to quickly try many common and short passwords (i.e. “brute-forcing”). If you use a simple password, which is a dictionary word, or it’s shorter than 8 symbols, your password is very easy to break for a determined individual.
Once the password has been hacked, an attacker can take over your e-mail, use your bank account or simply steal private data – like in the case of the Hollywood celebrities, whose private photos have been stolen from iCloud.
How to protect yourself:
- Use a long password which isn’t a dictionary word. Use a combination of letters, digits and special symbols. Don’t make life easy for hackers.
- Use a password manager that generates and remembers long passwords for you.
7. Bluetooth

Bluetooth networking is physically limited to only 10-15 meters, so it’s not a common threat. Still, an attacker can impersonate a bluetooth device that your phone is already paired with (such as a bluetooth headset). If they managed to pair with your phone, they can potentially intercept your calls. This technique is known as bluebugging.
Some companies even sell “bluetooth spy” software, though these products are a scam designed to quickly separate a naive spy from his money.
How to protect yourself:
- Don’t leave bluetooth on at all times.
- Like in real life, be careful of who you pair with.
8. Server leaks and hacks

Even if you’re very careful with securing your computer and phone, your data still lives somewhere in the cloud. Where it can be hacked. News are full of stories about hackers stealing millions of email passwords from here and thousands of social security accounts from there.
100% security for servers that support the cloud is never possible, because there many people whose livelihood depends on finding holes and backdoors. Strong IT companies, such as Google or Apple, don’t have a history of leaking sensitive data, but other companies with less resources are vulnerable.
How to protect yourself:
Basically, you cannot. The only consolation is that if your credit card or bank account details are stolen and it’s the financial company’s fault, you get immediately compensated.
9. Social Engineering
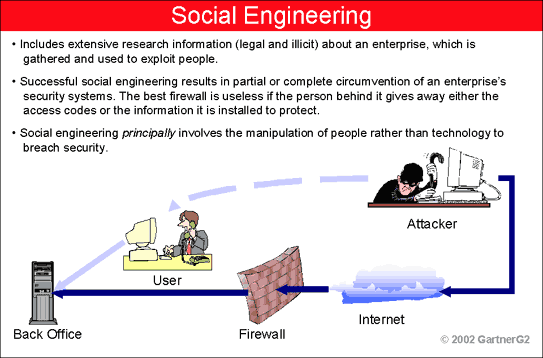
Social engineer is a hacker who asks for your password nicely.
“Hi, I’m Ross from Gmail support. We have a maintenance planned for tomorrow and you should change your password by clicking on _this_ link”.
That’s a hacker trying to socially engineer you to click on a phishing site and enter your password so that they can steal it. Spam emails such as the one quoted above are crude attempts, but hackers skillful in social engineering can be very persuasive. They can use the right words, their “From” e-mail address will look legit, and they will give you a myriad reasons for giving them the password to your website or similar.
How to protect yourself:
Don’t trust them.
10. Rogue cellular phone

They pulled this one… but what about the others?
Some lesser known cellphone brands come with preloaded spyware that steals your data. Even a big, established brand like Xiaomi has been accused of this behavior.
We believe that, unless you have plans to topple the Chinese government, you’re safe with Xiaomi. The problem is with the cheapest phones and tablets, and also with copycat cellphones. Don’t trust a fake Samsung phone with your sensitive data. The people who make money from ripping off Samsung will probably steal your data too.
How to protect yourself:
- Don’t use no-name phones and tablets. If you do, don’t enter any passwords or sensitive information into them.
Don’t let them spy on your mobile!
We hope that you’re now more conscious of the different ways your mobile data could be stolen and spied on. Like anything in life, it cannot be prevented with 100% certainty. But simple measures will make your mobile more secure and your online life less vulnerable to snooping.












You must be logged in to post a comment Login